git config --global user.name "FIRST_NAME LAST_NAME"
git config --global user.email "MY_NAME@example.com"
git config --global user.name "FIRST_NAME LAST_NAME"
git config --global user.email "MY_NAME@example.com"
Prerequisites:
– Disable swap
– Disable SElinux
– Disable Firewalld(optional if all k8 rule added)
Servers IP:
kmaster1 = 192.168.0.10
knode1 = 192.168.0.11
knode2 = 192.168.0.12
#Disable swap
swapoff -a
swapline=$(cat -n /etc/fstab | grep swap | awk '{print $1}')
if [ $(cat /etc/fstab | grep swap | awk '{print substr($0,0,1)}') != "#" ]
then
sed -i ""$swapline"s/.*/#&/" /etc/fstab
fi
#Disable SElinux
setenforce 0
sed -i 's/^SELINUX=enforcing$/SELINUX=permissive/' /etc/selinux/config
#Disable firewalld
systemctl stop firewalld
systemctl disable firewalld
#iptables conf
echo 'net.bridge.bridge-nf-call-ip6tables = 1
net.bridge.bridge-nf-call-iptables = 1' > /etc/sysctl.d/k8.conf
sysctl --systemAdd Kubernetes Repository
echo '[kubernetes]
name=Kubernetes
baseurl=https://packages.cloud.google.com/yum/repos/kubernetes-el7-x86_64
enabled=1
gpgcheck=1
repo_gpgcheck=1
gpgkey=https://packages.cloud.google.com/yum/doc/yum-key.gpg https://packages.cloud.google.com/yum/doc/rpm-package-key.gpg
' > /etc/yum.repos.d/kubernetes.repoOn kmaster01
yum install -y kubelet kubeadm kubectl docker
systemctl enable kubelet
systemctl start kubelet
systemctl enable docker
systemctl start docker
hostnamectl set-hostname kmaster01
kubeadm init
At end of above command run below command and save the join command.
mkdir -p $HOME/.kube
sudo cp -i /etc/kubernetes/admin.conf $HOME/.kube/config
sudo chown $(id -u):$(id -g) $HOME/.kube/config
AND note the join command
Apply weave network:
kubectl apply -f "https://cloud.weave.works/k8s/net?k8s-version=$(kubectl version | base64 | tr -d '\n')"On knode1:
yum install -y kubelet kubeadm kubectl docker
systemctl enable kubelet
systemctl start kubelet
systemctl enable docker
systemctl start docker
hostnamectl set-hostname knode1
#Join command
kubeadm join 192.168.0.10:6443 --token lfh49o.f9na1435g8vs1fmt \
--discovery-token-ca-cert-hash sha256:0064f08a4c0ef36e454b683f61a68e0bf78d9cdb45f7905128c68b28fc2a5b3eOn knode2:
yum install -y kubelet kubeadm kubectl docker
systemctl enable kubelet
systemctl start kubelet
systemctl enable docker
systemctl start docker
hostnamectl set-hostname knode2
#Join command
kubeadm join 192.168.0.10:6443 --token lfh49o.f9na1435g8vs1fmt \
--discovery-token-ca-cert-hash sha256:0064f08a4c0ef36e454b683f61a68e0bf78d9cdb45f7905128c68b28fc2a5b3enginx-app.yml
apiVersion: apps/v1
kind: Deployment
metadata:
name: my-nginx
spec:
selector:
matchLabels:
run: my-nginx
replicas: 2
template:
metadata:
labels:
run: my-nginx
spec:
containers:
- name: my-nginx
image: nginx
ports:
- containerPort: 80nginx-svc.yml
apiVersion: v1
kind: Service
metadata:
name: nginx-svc
labels:
run: nginx-svc
spec:
type: NodePort
ports:
- port: 80
protocol: TCP
selector:
run: my-nginxkubectl apply -f ngix-app.yml
kubectl apply -f ngix-svc.yml
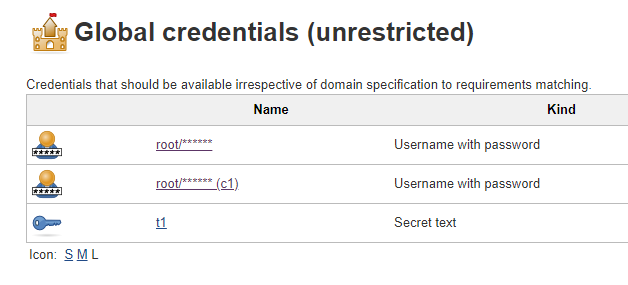
pipeline
{
agent { label 'master' }
stages
{
stage('check_credentials')
{
steps
{
withCredentials([usernamePassword(credentialsId: 'c1', usernameVariable: 'uname', passwordVariable: 'upass' )])
{
sh '''
echo "usernamePassword = $uname $upass" > test.txt
'''
}
withCredentials([usernameColonPassword(credentialsId: 'c1', variable: 'uname')])
{
sh '''
echo "usernameColonPassword = $uname" >> test.txt
'''
}
withCredentials([string(credentialsId: 't1', variable: 'TOKEN')])
{
sh '''
echo "string = $TOKEN" >> test.txt
'''
}
sh 'cat test.txt'
}
}
}
}
sample log :
abc-xyz 123
abc-xyz 123
abc-xyz 123
Sending logs to sample log ELK server:
echo -n "abc-xyz 123" >/dev/tcp/ELK_SERVER_IP/2001custom1.conf
input {
tcp
{
port => 2001
type => "syslog"
}
}
filter {
grok {
match => {"message" => "%{WORD:word1}-%{WORD:word2} %{NUMBER:number1}"}
}
#add tag
mutate {
add_tag => { "word1" => "%{word1}" }
}
#add custom field
mutate {
add_field => { "logstype=" => "sample" }
}
}
output {
if [type] == "syslog" {
elasticsearch {
hosts => ["localhost:9200"]
index => "custom1-%{+YYYY.MM.dd}"
}
#for debug
#stdout {codec => rubydebug}
}
}Run logstash to collect the logs
logstash -f custom1.confNOTE:
– if number1 was already indexed as string then you have to delete the old index
– if use add_field again with same name after grok it will show double value
CURL
curl -s http://USERNAME:USER_API_TOKEN@localhost:8080/job/task1/config.xml | curl -X POST 'http://USERNAME:USER_API_TOKEN@localhost:8080/createItem?name=job1' --header "Content-Type: application/xml" -d @-Jenkins-cli
java -jar jenkins-cli.jar -s http://localhost:8080/create-job NAME_OF_JOB < job.xmlBelow command will host current directory as http server on specified port
Python2:
python -m SimpleHTTPServer <port_number>
python3:
python3 -m http.server <port_number>What’s LXC?
– API to communicate with with LXD(Linux container)
What’s LXD?
– It’s like VM for Linux containers
yum -y install epel-release
yum -y install libvirt lxc lxc-templates libcap-devel libcgroup busybox wget bridge-utils lxc-extra
systemctl start libvirtd
systemctl enable libvirtd[root@lxc01~]# lxc-checkconfig
Kernel configuration not found at /proc/config.gz; searching...
Kernel configuration found at /boot/config-3.10.0-862.el7.x86_64
--- Namespaces ---
Namespaces: enabled
Utsname namespace: enabled
Ipc namespace: enabled
Pid namespace: enabled
User namespace: enabled
newuidmap is not installed
newgidmap is not installed
Network namespace: enabled
Multiple /dev/pts instances: enabled
--- Control groups ---
Cgroup: enabled
Cgroup clone_children flag: enabled
Cgroup device: enabled
Cgroup sched: enabled
Cgroup cpu account: enabled
Cgroup memory controller: enabled
Cgroup cpuset: enabled
--- Misc ---
Veth pair device: enabled
Macvlan: enabled
Vlan: enabled
Bridges: enabled
Advanced netfilter: enabled
CONFIG_NF_NAT_IPV4: enabled
CONFIG_NF_NAT_IPV6: enabled
CONFIG_IP_NF_TARGET_MASQUERADE: enabled
CONFIG_IP6_NF_TARGET_MASQUERADE: enabled
CONFIG_NETFILTER_XT_TARGET_CHECKSUM: enabled
--- Checkpoint/Restore ---
checkpoint restore: enabled
CONFIG_FHANDLE: enabled
CONFIG_EVENTFD: enabled
CONFIG_EPOLL: enabled
CONFIG_UNIX_DIAG: enabled
CONFIG_INET_DIAG: enabled
CONFIG_PACKET_DIAG: enabled
CONFIG_NETLINK_DIAG: enabled
File capabilities: enabled
Note : Before booting a new kernel, you can check its configuration
usage : CONFIG=/path/to/config /usr/bin/lxc-checkconfig
lxc-create -n centos7container -t centosIt will pull the centos container image from the internet and will use the centos template from /usr/share/lxc/templates/
lxc-start -n centos7container -d[root@lxc01 ~]# lxc-ls
centos7container
[root@lxc01 ~]# lxc-ls --active
centos7container
lxc-attach -n centos7containerlxc-stop -n centos7container
lxc-destroy -n centos7containerFast: dd if=/dev/zero of=out.img bs=1m iflag=fullblock,count_bytes count=1G
Faster(kind of): truncate -s 1G out.img
Fastest : fallocate -l 1G out.img
Jenkinsfile
pipeline
{
agent any
stages
{
stage('build')
{
steps
{
script
{
//first.groovy path might change as per your need
def var1 = load "first.groovy"
var1.build("php build")
}
sh '''
echo "build"
'''
}
}
stage('deploy')
{
steps
{
script
{
def var2 = load "first.groovy"
var2.build("php deploy")
}
sh '''
echo "deploy"
'''
}
}
}
}first.groovy
def build(String arg1) {
sh """
echo "from build function : ${arg1}"
"""
}
def deploy(String arg2) {
sh """
echo "from deploy function : ${arg2}"
"""
}
return this
Output:
Running on Jenkins in /var/lib/jenkins/workspace/initedit/ss
[Pipeline] {
[Pipeline] stage
[Pipeline] { (build)
[Pipeline] script
[Pipeline] {
[Pipeline] load
[Pipeline] { (first.groovy)
[Pipeline] }
[Pipeline] // load
[Pipeline] sh
+ echo 'from build function : php build'
from build function : php build
[Pipeline] }
[Pipeline] // script
[Pipeline] sh
+ echo build
build
...........git fetch --all
OR
git remote updateNote: It will not update local repo.
To pull all branch
git pull --allNote: It will update local repo.